How do I forward a Splunk log
Download and install the Splunk Universal Forwarder on the Code42 server or device that contains the logs you wish to forward. Configure the Splunk Universal Forwarder to target your Splunk Enterprise server. Configure the Splunk Universal Forwarder to monitor log files on your Code42 server or device.
How do I configure a Splunk forwarder on Linux?
- Step 1: Download Splunk Universal Forwarder: …
- Step 2: Install Forwarder.
- Step 3: Enable boot-start/init script: …
- Step 4: Enable Receiving input on the Index Server. …
- Step 5: Configure Forwarder connection to Index Server: …
- Step 6: Test Forwarder connection: …
- Step 7: Add Data:
How do I send pod logs to Splunk?
- STEP 1: Create a persistent volume.
- STEP 2: Deploy an app and mount the persistent volume.
- STEP 3: Create a configmap.
- STEP 4: Deploy the splunk universal forwarder.
- STEP 5: Check if logs are written to splunk.
How do I forward data from Splunk cloud?
- Download and install the universal forwarder software.
- Download the Splunk universal forwarder credentials package.
- Install the Splunk universal forwarder credentials package on the universal forwarder machine.
How do I Forward Windows event logs to Splunk?
- Click Settings > Data Inputs.
- Click Local event log collection.
- Click New to add an input.
How do I activate Splunk forwarder?
- Configure receiving on a Splunk Enterprise instance or cluster.
- Download and install the universal forwarder.
- Start the universal forwarder and accept the license agreement. …
- (Optional) Change the credentials on the universal forwarder from their defaults.
How do I deploy a Splunk forwarder?
- Download Splunk Universal Forwarder 8.0. …
- Install the Splunk Universal Forwarder by entering the following command. …
- Start the Splunk Universal Forwarder. …
- Add forward server details (the receiver host and port in Splunk). …
- Edit the inputs. …
- Restart the Splunk Universal Forwarder. …
- Verify if data is flowing to Splunk.
How do I transfer data to Splunk forwarder?
- Configure a Splunk Enterprise host to receive the data.
- Determine the kind of forwarder you want to put on the host with the data.
- Download Splunk Enterprise or the universal forwarder for the platform and architecture of the host with the data.
- Install the forwarder onto the host.
How do I check Splunk forwarder status in Linux?
- Monitor remote Windows event logs.
- Configure a Splunk forwarder on Linux.
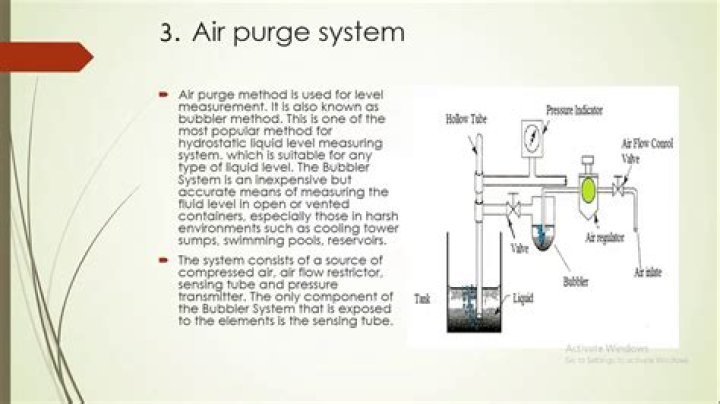
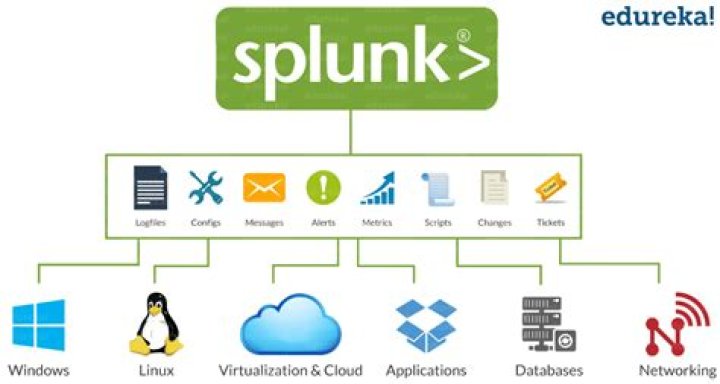
The Splunk universal forwarder is a free, dedicated version of Splunk Enterprise that contains only the essential components needed to forward data. TechSelect uses the universal forwarder to gather data from a variety of inputs and forward your machine data to Splunk indexers. The data is then available for searching.
Article first time published onWhat is Splunk intermediate forwarder?
intermediate forwarder A forwarder that you have configured to receive data from one or more forwarders and subsequently send that data to either an indexer or another forwarder. … You want to transform any data before sending it to an indexer without having the final receiving indexer do any of the transforming work.
How install Splunk on UNIX and Linux?
You can install the add-on onto any type of Splunk Enterprise or Splunk Cloud Platform instance. Get the Splunk Add-on for Unix and Linux by downloading it from or browsing to it using the app browser within Splunk Web.
What is syslog in Splunk?
Splunk Connect for Syslog is an open source packaged solution for getting data in to Splunk. It is based on the syslog-ng Open Source Edition (Syslog-NG OSE) and transports data to Splunk via the Splunk HTTP event Collector (HEC) rather than writing events to disk for collection by a Universal Forwarder.
Can Splunk act as a syslog server?
Splunk Connect for Syslog is a containerized Syslog-ng server with a configuration framework designed to simplify getting syslog data into Splunk Enterprise and Splunk Cloud. This approach provides an agnostic solution allowing administrators to deploy using the container runtime environment of their choice.
What are Splunk logs?
Splunk is centralized logs analysis tool for machine generated data, unstructured/structured and complex multi-line data which provides the following features such as Easy Search/Navigate, Real-Time Visibility, Historical Analytics, Reports, Alerts, Dashboards and Visualization.
How install Splunk on Kubernetes?
- kubectl apply -f
- $ kubectl get pods NAME READY STATUS RESTARTS AGE splunk-operator-75f5d4d85b-8pshn 1/1 Running 0 5s.
What is input conf in Splunk?
conf. You can use the inputs. conf file to monitor files and directories with the Splunk platform. The inputs.
What is whitelist in Splunk?
“When you specify wildcards in a file input path, Splunk creates an implicit whitelist for that stanza. The longest fully qualified path becomes the monitor stanza, and the wildcards are translated into regular expressions, as listed in the table above.”
What is Splunk deployment server?
A deployment server is a Splunk Enterprise instance that acts as a centralized configuration manager for any number of other instances, called “deployment clients”. … Deployment clients can be universal forwarders, heavy forwarders, indexers, or search heads. Each deployment client belongs to one or more server classes.
What is a deployment client in Splunk?
deployment client A Splunk Enterprise instance that is remotely configured by a deployment server. Deployment clients can be grouped together into one or more server classes. Each deployment client periodically polls its deployment server.
What is forwarder management?
The forwarder management interface is an interactive, visual tool for creating server classes, which map deployment clients to deployment apps. You can also use forwarder management to manage and monitor your deployment. The interface saves server class configurations to a serverclass.
Which of the Splunk components is connected with deployment server *?
The deployment client (the forwarder) connects to the Splunk management port (default 8089) on the deployment server.
How do I enable Splunk?
- Log into Splunk Enterprise on the indexer.
- In the system bar, click Settings > Forwarding and Receiving. …
- Under “Receive Data” click Configure Receiving.
- Click New.
How do I restart Splunk forwarder?
In Splunk Web, go to Settings > Server controls. Select “Restart Splunk“
How do I know if my Splunk forwarder is working?
- check if splunk process is running on splunk forwarder. …
- check if splunk forwarder forwarding port is open by using below command. …
- Check on indexer if receiving is enabled on port 997 and port 997 is open on indexer. …
- check if you are able to ping indexer from forwarder host.
How do I start Splunk in Linux?
- Log-in as splunk : sudo su – splunk;
- Check the current directory after log-in : pwd; # must be : /opt/splunk , if so , proceed.
- Start the daemon : bin/splunk start # you will asked to agree the license => agree if you want to start daemon.
- Waiting for the following message :
Where are Splunk logs stored?
Splunk software keeps track of its activity by logging to various files located in /opt/$SPLUNK_HOME/var/log/splunk.
Where is Splunk forwarder installed?
The universal forwarder installs by default in the /opt/splunkforwarder directory. The default installation directory for Splunk Enterprise is /opt/splunk .
How do I transfer data to Splunk cloud?
- Splunk Cloud Platform and the forwarder credentials app.
- Use a deployment server to deliver configurations to multiple forwarders.
- Work with an intermediate forwarding tier.
- Use a universal forwarder to get data into Splunk Cloud Platform.
How does Splunk Cloud Connect to heavy forwarder?
- Download the Heavy Forwarder.
- Install, ./splunk enable boot-start.
- Configure the HWF to receive data.
- Configure the HWF to send data to indexer ( ./splunk add forward-server customer.splunkcloud.com:9997)
- Download your Universal Forwarder app from your Splunk Cloud instance.
How do I upload data to Splunk cloud?
- Go to the Splunk Light Search view. …
- Under Data, click Add Data.
- In the Add Data view, click Upload.
- Click Select File to browse for your CSV file, or drag-and-drop the file into the outlined box. …
- Click Next.
- (Optional) Review your data in the Set Sourcetype view.
- Click Next.