How does a rail fence cipher work
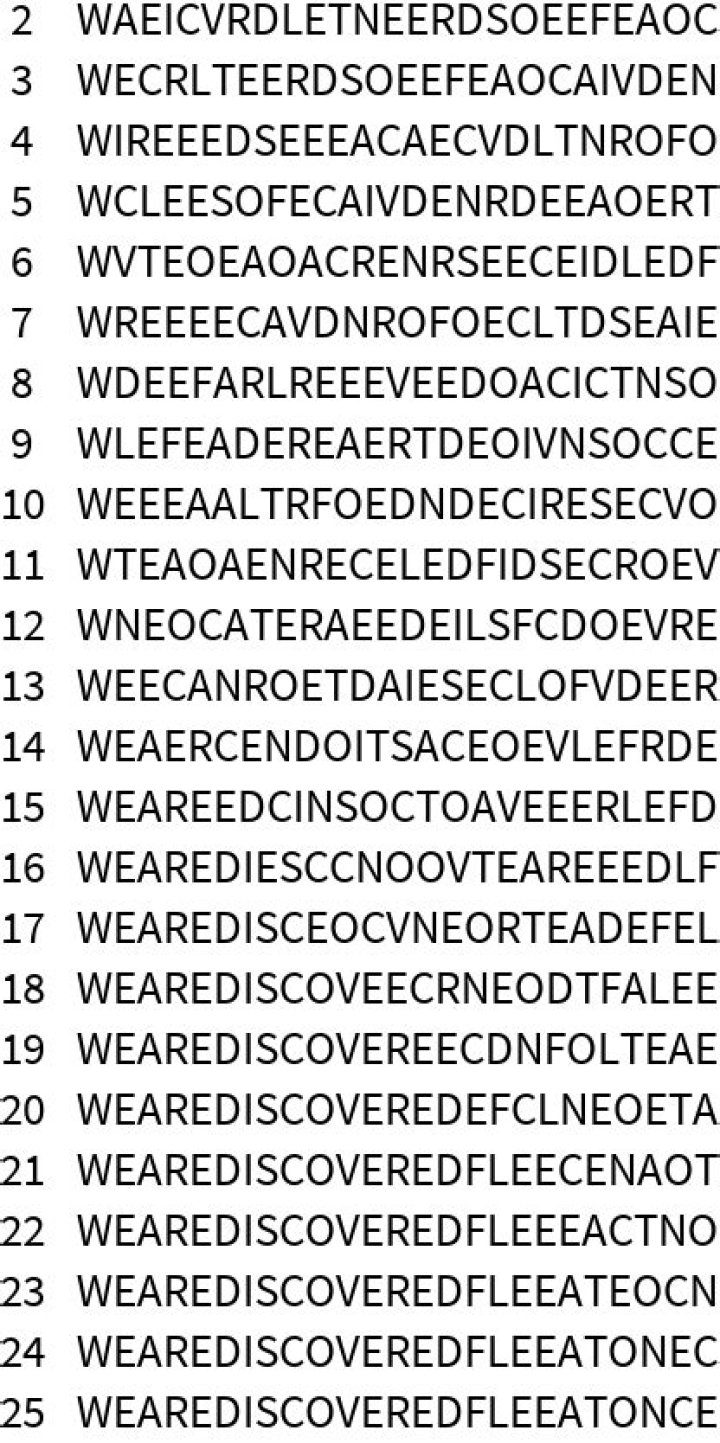
The rail fence cipher (sometimes called zigzag cipher) is a transposition cipher that jumbles up the order of the letters of a message using a basic algorithm. The rail fence cipher works by writing your message on alternate lines across the page, and then reading off each line in turn.
How does rail fence algorithm work?
Encryption. In the rail fence cipher, the plaintext is written downwards diagonally on successive “rails” of an imaginary fence, then moving up when the bottom rail is reached, down again when the top rail is reached, and so on until the whole plaintext is written out. The ciphertext is then read off in rows.
Who created the rail fence cipher?
The Rail Fence Cipher was invented in ancient times. It was used by the Greeks, who created a special tool, called scytale, to make message encryption and decryption easier. Currently, it is usually used with a piece of paper.
What is the purpose of a rail fence cipher?
A rail fence cipher is a type of written code or cipher that allows its users to transform text for the purposes of encoding, using only a pencil and paper.How does substitution cipher work?
Substitution ciphers encrypt the plaintext by swapping each letter or symbol in the plaintext by a different symbol as directed by the key. … Spaces in the ciphertext are just added for readability; they would be removed in a real application of the cipher to make attacking the ciphertext more difficult.
What is the formula for decryption in Hill cipher?
Decryption. Decrypting with the Hill cipher is built on the following operation: D(K, C) = (K-1 *C) mod 26 Where K is our key matrix and C is the ciphertext in vector form. Matrix multiplying the inverse of the key matrix with the ciphertext produces the decrypted plaintext.
What is the type of rail fence technique?
In the rail fence cipher, the plain-text is written downwards and diagonally on successive rails of an imaginary fence. When we reach the bottom rail, we traverse upwards moving diagonally, after reaching the top rail, the direction is changed again. Thus the alphabets of the message are written in a zig-zag manner.
What is the difference between a block cipher and a stream cipher?
The main difference between a Block cipher and a Stream cipher is that a block cipher converts the plain text into cipher text by taking plain text’s block at a time. While stream cipher Converts the plain text into cipher text by taking 1 byte of plain text at a time.How do you use a bacon cipher?
LetterCodeBinaryCaaaba00010Daaabb00011Eaabaa00100Faabab00101
Which block is cipher?A block cipher is an encryption method that applies a deterministic algorithm along with a symmetric key to encrypt a block of text, rather than encrypting one bit at a time as in stream ciphers. For example, a common block cipher, AES, encrypts 128 bit blocks with a key of predetermined length: 128, 192, or 256 bits.
Article first time published onHow does route cipher work?
The Route Cipher is a transposition cipher. It rearranges the plaintext letters based on a shape of an imaginary path drawn on a grid.
What is myszkowski cipher?
The Myszkowski Transposition Cipher is a variant of Columnar Transposition in the way it deals with recurring letters in the keyword. It was proposed by Émile Victor Théodore Myszkowski in 1902. The same methodology as for Columnar Transposition is used, where the plaintext is written out in rows under the keyword.
What is the scytale cipher?
Scytale is a very basique transposition cipher used in ancient Greece and by spartans. A band is wrapped around a rod, a message is written, and when the band is unrolled a ciphertext appears.
Is rail fence a substitution cipher?
The Rail Fence Cipher is a type of transposition cipher. … This is in contrast to a substitution cipher, in which the plaintext letters are replaced by letters from another alphabet (or by different letters from the same alphabet).
Is the rail fence cipher secure?
It is a transposition cipher that follows a simple rule for mixing up the characters in the plaintext to form the ciphertext. The railfence cipher offers essentially no communication security, and it will be shown that it can be easily broken even by hand.
How do you decode a columnar cipher?
To decipher it, the recipient has to work out the column lengths by dividing the message length by the key length. Then, write the message out in columns again, then re-order the columns by reforming the key word.
How do you decrypt substitution ciphertext?
- Scan through the cipher, looking for single-letter words. …
- Count how many times each symbol appears in the puzzle. …
- Pencil in your guesses over the ciphertext. …
- Look for apostrophes. …
- Look for repeating letter patterns. …
- Try to decipher two-, three-, and four-letter words. …
- Scan for double letters.
How does mixing ciphers impact the level of difficulty of decrypting the ciphertext?
How does mixing ciphers impact the level of difficulty of decrypting the ciphertext? Using a mix of ciphers makes it much harder to decrypt a ciphertext because if there is just one cipher, if you find the key to one letter, you can apply it to the entire message.
How do you code a substitution cipher?
Substitution ciphers work by creating a disordered alphabet, allowing you to substitute letters for other letters. For a straightforward substitution cipher, simply use the alphabet backwards, so that “a” becomes “z,” “b” becomes “y,” “c” becomes “x,” and so on.
How many different keys are possible in Hill cipher?
Notice that if four four-block plaintext/ciphertext correspondences are known, then the resulting system of linear equations can be solved for the 16 entries in the encryption key. 12,303,585,972,327,392,870,400 possible keys. In a 1931 paper – also in the Monthly – Hill extends his ideas.
What is polygraphic substitution cipher?
Polygraphic substitution is a cipher in which a uniform substitution is performed on blocks of letters. When the length of the block is specifically known, more precise terms are used: for instance, a cipher in which pairs of letters are substituted is bigraphic.
How many combinations of keys can be constructed from a 72 ciphertext stream cipher?
9. How many combinations of keys can be constructed from a 72 ciphertext stream cipher? Explanation: For stream cipher, if there are n ciphertexts then there are n*(n−1)/2 combination of keys to be made. = 2556.
Who created Bacon cipher?
In 1623, Francis Bacon created a cipher system using the techniques of substitution and steganography – the art of writing hidden messages in such a way that no one apart form the sender and receiver know of its existence. We describe his system using binary notation (rather than the a-b notation he used).
Which cipher contains dagger?
How to recognize Gold-Bug ciphertext? The ciphered message contains the characters † or ‡ (dagger and double dagger) and the 8 appears often. The index of coincidence is similar to the language of the plain text.
Are all block ciphers Polyalphabetic explain?
Block ciphers work in a way similar to polyalphabetic ciphers, with the exception that a block cipher pairs together two algorithms for the creation of ciphertext and its decryption. … Each algorithm uses two inputs: a key and a “block” of bits, each of a set size.
What are the two approaches to attacking a cipher?
There are two general approaches to attacking a conventional encryption scheme: Cryptanalysis (cryptanalytic attacks): This attack relies on the nature of the algorithm plus some knowledge of the general characteristics of the plaintext or some sample plaintext–ciphertext pairs.
Why are block ciphers more secure?
We can simply say that the design philosophy of block ciphers are more enhanced and so it seems it is easier to design a secure block cipher. … A block cipher in counter mode creates the keystream in blocks. And then it XORs that keystream with the plaintext of the message to be encrypted.
What is CBC mode of DES?
The Cipher Block Chaining (CBC) mode is a typical block cipher mode of operation using block cipher algorithm. In this version, we provide Data Encryption Standard (DES) and Advanced Encryption Standard (AES) processing ability, the cipherkey length for DES should be 64 bits, and 128/192/256 bits for AES.
In which cipher a pair of keys is used?
Asymmetric Key Cryptosystems In asymmetric key cryptography, the decryption key is different than the key that was used to encrypt the message. Each party taking part in the communication stream in an asymmetric key cryptosystem has a pair of keys, known as the public key and the private key.
How is cipher feedback used?
Ciphertext feedback (CFB) is a mode of operation for a block cipher. In contrast to the cipher block chaining (CBC) mode, which encrypts a set number of bits of plaintext at a time, it is at times desirable to encrypt and transfer some plaintext values instantly one at a time, for which ciphertext feedback is a method.
How can Transpositional ciphers be attacked?
(4) in their paper presented three optimization heuristics which can be utilized in attacks on the transposition cipher, These heuristics are simulated annealing, genetic algorithm and tabu search.