How does Kerberos generate Keytab
Log on as theKerberos administrator (Admin) and create a principal in the KDC. You can use cluster-wide or host-based credentials. … Obtain the key of the principal by running the subcommand getprinc principal_name .Create the keytab files, using the ktutil command:
Where is the Keytab file?
On application servers that provide Kerberized services, the keytab file is located at /etc/krb5/krb5. keytab , by default. A keytab is analogous to a user’s password. Just as it is important for users to protect their passwords, it is equally important for application servers to protect their keytab files.
How do I read a Kerberos keytab file?
- Become superuser on the host with the keytab file. Note – …
- Start the ktutil command. # /usr/bin/ktutil.
- Read the keytab file into the keylist buffer by using the read_kt command. …
- Display the keylist buffer by using the list command. …
- Quit the ktutil command.
What does a Keytab look like?
A keytab contains one or more entries, where each entry consists of a timestamp (indicating when the entry was written to the keytab), a principal name, a key version number, an encryption type, and the encryption key itself. A keytab can be displayed using the klist command with the -k option.What is Keytab principal?
A keytab is a file containing pairs of Kerberos principals and encrypted keys (which are derived from the Kerberos password). … Keytab files are commonly used to allow scripts to automatically authenticate using Kerberos, without requiring human interaction or access to password stored in a plain-text file.
How do I find my Keytab?
The contents of keytab file can be verified using either Unix/linux ktutil or klist commands or java ktab utility. Alternatively you can also use Klist or Ktab utility that comes with standard java. Key tab: krba01.
How is Keytab file created?
Create the keytab files, using the ktutil command: Create a keytab file for each encryption type you use by using the add_entry command. For example, run ktutil: add_entry -password -p principal_name -k number -e encryption_type for each encryption type.
How do I add a Keytab to Kerberos?
- Make sure that the principal already exists in the Kerberos database. …
- Become superuser on the host that needs a principal added to its keytab file.
- Start the kadmin command. …
- Add a principal to a keytab file by using the ktadd command. …
- Quit the kadmin command.
How do I get Keytab?
- Log in to any cluster VM.
- From the command line, type. ktutil. …
- Type the following command: addent -password -p <user name> -k 1 -e RC4-HMAC. …
- When prompted, enter the password for the Kerberos principal user.
- Type the following command to create a keytab: …
- Type.
A Kerberos Principal represents a unique identity in a Kerberos system to which Kerberos can assign tickets to access Kerberos-aware services. Principal names are made up of several components separated by the “/” separator. You can also specify a realm as the last component of the name by using the “@” character.
Article first time published onHow long is a Keytab valid?
Keytab does expire, independently of Kerberos password. For example in Linux, the default lifespan of keytab is 24 hours. Once the keytab file expires, user has to request a new keytab file. See screenshot below.
Is Keytab host specific?
Keytabs are not host specific. They are equivalent of passwords. Microsoft recommends one keytab per application. In such case, if there are two different applications running on two different hosts, the same keytab won’t work on both hosts.
How do I decode a Keytab file?
- Do one of the following: (UNIX) Enter the following: <utilityPath>/klist -t -k /opt/bmc/bladelogic/NSH/br/blauthsvc.keytab. Copy. …
- The klist utility displays output similar to the following: Service principal: blauthsvc/[email protected] Copy.
What is Kvno in Keytab?
Sometimes, the key version number (KVNO) used by the KDC and the service principal keys stored in /etc/krb5/krb5. keytab for services hosted on the system do not match. The KVNO can get out of synchronization when a new set of keys are created on the KDC without updating the keytab file with the new keys.
What is IPA Keytab?
A keytab is a file with one or more secrets (or keys) for a Kerberos principal. A Kerberos service principal is a Kerberos identity that can be used for authentication. Service principals contain the name of the service, the hostname of the server, and the realm name.
What is Ktutil?
DESCRIPTION. The ktutil command is an interactive command-line interface utility for managing the keylist in keytab files. You must read in a keytab’s keylist before you can manage it. Also, the user running the ktutil command must have read/write permissions on the keytab.
What is Kinit Kerberos?
kinit is used to obtain and cache Kerberos ticket-granting tickets. This tool is similar in functionality to the kinit tool that are commonly found in other Kerberos implementations, such as SEAM and MIT Reference implementations.
How do I know if Kerberos is installed?
Open Activity Monitor in the Utilities folders, set it to display All Processes, list by Name and look for “Kerberos” in the list. Kerberos is not a single process but the name of acomputer network authentication protocol developed at MIT.
What creates etc krb5 Keytab?
The keytab is generated by running kadmin and issuing the ktadd command.
How do you create a Keytab on a Mac?
- Log in to the KDC using your Kerberos service account credentials.
- Open a command prompt and then enter the following command: ktpass /princ <principal_name> /pass <password> /crypto <algorithm> /ptype KRB5_NT_PRINCIPAL /out <file_name>.keytab. The. <principal_name> and. <password>
Why do we need Keytab file?
The purpose of the Keytab file is to allow the user to access distinct Kerberos Services without being prompted for a password at each Service. Furthermore, it allows scripts and daemons to login to Kerberos Services without the need to store clear-text passwords or for human intervention.
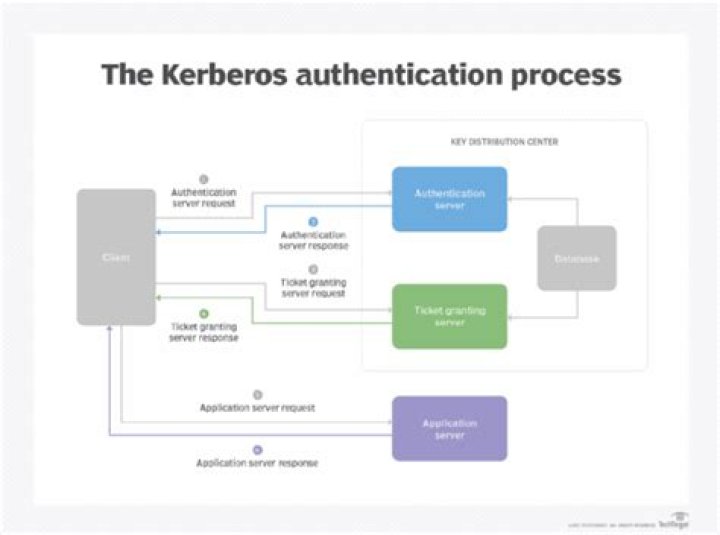
What are the 3 main parts of Kerberos?
Kerberos has three parts: a client, server, and trusted third party (KDC) to mediate between them. Clients obtain tickets from the Kerberos Key Distribution Center (KDC), and they present these tickets to servers when connections are established.
What is Kerberos Sname?
cname — contains the user name being authenticated. realm — contains the Kerberos realm (a.k.a. Windows domain name) sname — the service name being requested (in this case, it is again the windows domain name) till — The requested expiration time of the ticket being requested.
How do I renew my Kerberos Keytab?
- Connect to the master node using SSH.
- To confirm that the ticket is expired, run the klist command. …
- To confirm the Kerberos principal name, list the contents of the keytab file: …
- To renew the Kerberos ticket, run kinit and specify both the keytab file and the principal: …
- Confirm that the credentials are cached:
How can I tell if a Keytab is valid?
You can use Kerberos utilities to verify that the SPNs and the keytab files are valid. You can also use the utilities to determine the status of the Kerberos Key Distribution Center (KDC). to view and verify the SPNs and keytab files.
How long does Kinit last?
You can separately specify how long your ticket will last before expiring, and how long it could last if you renew it before that expiration, with “kinit -l lifetime -r renewable_life”, but note that the maximum is 9 hours for lifetime and 7 days for renewable life, and our defaults will already request these maximum …
Is Keytab file encrypted?
4.3. 3 The Keytab File The keytab file is an encrypted, local, on-disk copy of the host’s key. The keytab file, like the stash file (Create the Database) is a potential point-of-entry for a break-in, and if compromised, would allow unrestricted access to its host.