Should I use salt with bcrypt

Another benefit of bcrypt is that it requires a salt by default. Let’s take a deeper look at how this hashing function works! “`bcrypt` forces you to follow security best practices as it requires a salt as part of the hashing process. Hashing combined with salts protects you against rainbow table attacks!
What does bcrypt stand for?
184 bit. Rounds. variable via cost parameter. bcrypt is a password-hashing function designed by Niels Provos and David Mazières, based on the Blowfish cipher and presented at USENIX in 1999.
Is bcrypt still safe?
BCrypt is a computationally difficult algorithm designed to store passwords by way of a one-way hashing function. … Bcrypt has been around since the late 90s and has handled significant scrutiny by the information security/cryptography community. It has proven reliable and secure over time.
What is a salt in a hash?
Salting is simply the addition of a unique, random string of characters known only to the site to each password before it is hashed, typically this “salt” is placed in front of each password. The salt value needs to be stored by the site, which means sometimes sites use the same salt for every password.What can I use instead of bcrypt?
If someone faces similar issue, you can try bcyrptjs which is optimized bcrypt written in JavaScript with zero dependencies and is also compatible to the C++ bcrypt.
How does bcrypt compare without salt?
Bcrypt compare hashed and plaintext passwords without the salt string because the hashed password contains the salt string which we created at the time of hashing. So in the above hashed password, There are three fields delimited by $ symbol.
Can you decrypt bcrypt?
You simply can’t. bcrypt uses salting, of different rounds, I use 10 usually. This 10 is salting random string into your password. To answer the original posters question…. to ‘decrypt’ the password, you have to do what a password cracker would do.
Where is bcrypt used?
It is used specifically encrypting and securely storing passwords. It is used primarily when a user enters a password and that password needs to be stored in a database in a way that the original password could not be guessed even if the system was attacked and the database got compromised.Can you crack bcrypt?
bcrypt is a very hard to crack hashing type, because of the design of this slow hash type that makes it memory hard and GPU-unfriendly (especially with high cost factors).
What is salting a password?In cryptography, a salt is random data that is used as an additional input to a one-way function that hashes data, a password or passphrase. Salts are used to safeguard passwords in storage. … Salting is one such protection. A new salt is randomly generated for each password.
Article first time published onWhy is bcrypt good?
Bcrypt can expand what is called its Key Factor to compensate for increasingly more-powerful computers and effectively “slow down” its hashing speed. Changing the Key Factor also influences the hash output, so this makes Bcrypt extremely resistant to rainbow table-based attacks.
Can we decrypt SHA256?
SHA256 is a hashing function, not an encryption function. Secondly, since SHA256 is not an encryption function, it cannot be decrypted.
What is salt and pepper encryption?
A pepper is similar in concept to a salt or an encryption key. … A pepper performs a comparable role to a salt or an encryption key, but while a salt is not secret (merely unique) and can be stored alongside the hashed output, a pepper is secret and must not be stored with the output.
What is salt and nonce?
A nonce is transitive. A salt is static. A nonce is used for a single scope, next time a different nonce is used. A salt is used every time you test to see that the hashed value is tested, so it must be the same every time.
Which is better SHA256 or bcrypt?
SHA-256, in particular, benefits a lot from being implemented on a GPU. Thus, if you use SHA-256-crypt, attackers will be more at an advantage than if you use bcrypt, which is hard to implement efficiently in a GPU.
Why is bcrypt so slow?
bcrypt is designed to be slow and not to allow any shortcut. It takes more effort to brute force attack the password. The slower the algorithm, the less guesses can be made per second. The extra time won’t be noticed by a user of the system, but will make it harder to crack the password.
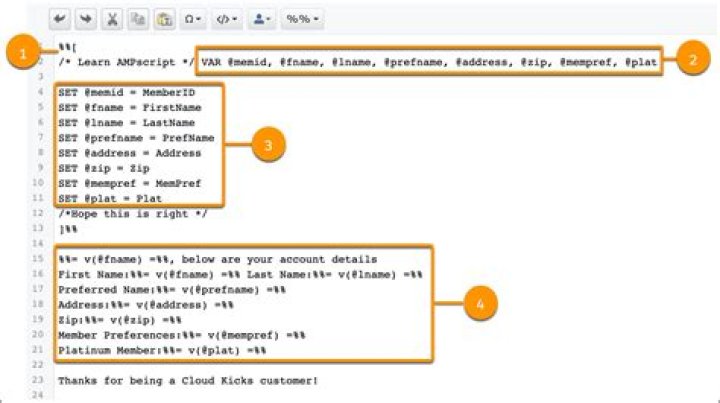
How do I use bcrypt in flask?
- app = Flask(__name__) bcrypt = Bcrypt(app)
- password = ‘hunter2’ pw_hash = bcrypt. generate_password_hash(password)
- candidate = ‘secret’ bcrypt. check_password_hash(pw_hash, candidate)
Is Bcrypt a hash or encryption?
Bcrypt is a password hashing function designed by Niels Provos and David Mazières, based on the Blowfish cipher, and presented at USENIX in 1999. Bcrypt is a cross platform file encryption utility. Encrypted files are portable across all supported operating systems and processors.
Should I use Bcrypt or Bcryptjs?
Conclusion. Bcrypt is way faster than bcryptjs, although users prefer bcryptjs at npm. Both libraries are excellent and easy to accomplish their purpose.
Is hashing and encryption the same?
Hashing and encryption are the two most important and fundamental operations of a computer system. … Hashing on an input text provides a hash value, whereas encryption transforms the data into ciphertext.
Is bcrypt reversible?
So, just like irreversible algorithms based cryptographic digests, bcrypt produces an irreversible output, from a password, salt, and cost factor. Its strength lies in Blowfish’s resistance to known plaintext attacks, which is analogous to a “first pre-image attack” on a digest algorithm.
Is bcrypt better than MD5?
First, no. Many sites allow login attempts without a rate limit. With MD5, assuming the servers can handle it, a user could very rapidly attempt to brute-force passwords just by trying lots of passwords in quick succession. bcrypt’s slowness guarantees that such an attempt will be much slower.
What is bcrypt Nodejs?
The bcrypt library on NPM makes it really easy to hash and compare passwords in Node. If you’re coming from a PHP background, these are roughly equivalent to password_hash() and password_verify(). Bcrypt is the de facto way to hash and store passwords.
Do you store the salt in the database?
The salt is not an encryption key, so it can be stored in the password database along with the username – it serves merely to prevent two users with the same password getting the same hash.
What is cost factor in bcrypt?
Bcrypt Cost Factor = 6 + (Number years of user membership or some factor thereof) with an optional ceiling for total cost, perhaps modified in some way by the login frequency of that user.
What does bcrypt compare return?
bcrypt. compare() always returns false whatever the password is correct or not, and whatever the password (I tried several strings). The password is only hashed once (so the hash is not re-hashed) on user’s creation. The password and the hash given to the compare method are the right ones, in the right order.
Can you brute force bcrypt?
Bcrypt: The strongest hashing type we tested. Bcrypt is a 184-bit hash created in 1999. It uses a salt to guard against rainbow table attacks and is adaptive. Over time, it becomes resistant to brute-force search attacks even with increasing computational power.
How do I make bcrypt faster?
- Divvy up the task and use more threads/processors/computers.
- Use a lower “complexity” factor. This will make the hashing faster, but decrease the security of the hashes somewhat, so not a very good option.
Can you Bruteforce bcrypt?
1 Answer. Bcrypt use a configurable iteration count, so the answer to your question is: whatever you want it to be. If the iteration count is such that one bcrypt invocation is as expensive as 10 computations of MD5, then brute-forcing the password will be 10 times more expensive with bcrypt than with MD5.
How long is a Bcrypt salt?
bcrypt uses a 128-bit salt and encrypts a 192-bit magic value. It takes advantage of the fact that the Blowfish algorithm (used in the core of bcrypt for password hashing) needs a fairly expensive key setup, thus considerably slowing down dictionary-based attacks.
What does salting DO network?
Salting is a concept that typically pertains to password hashing. Essentially, it’s a unique value that can be added to the end of the password to create a different hash value. This adds a layer of security to the hashing process, specifically against brute force attacks.