What are hardening techniques
Network hardening techniques include properly configuring and securing network firewalls, auditing network rules and network access privileges, disabling certain network protocols and unused or unnecessary network ports, encrypting network traffic, and disabling network services and devices not currently in use or …
What is an example of application hardening?
For example, users can jailbreak or root their device, which disables the operating system’s safeguards. Therefore, application hardening is an important part of mobile application security, because it builds protections into the app itself regardless of the security status of the device or operating system.
What are the ways you can think of to harden your applications if you are a software developer?
- Allowing installation only from trusted application repositories such as the Microsoft Store.
- Automated patches of standard and third-party applications.
- Firewalls, antivirus, and malware or spyware protection programs.
- Software-based data encryption.
What is user application hardening?
Application hardening refers to preventing the running of malware or unwanted code, by turning off unnecessary features in applications. The Essential Eight’s recommendation revolves around hardening the web browser and Microsoft Office to configure web browsers to block or disable unneeded features.What is device hardening?
Device hardening simply refers to the process of reducing vulnerabilities in your security devices. It is a necessary step that ought to be taken even before the devices are installed in the network, so that when they are finally in use, they do not have any potential loopholes which can be exploited by hackers.
What strategies are used in hardening Windows 2000 OS and its file system?
- Disable all unnecessary services. …
- Remove all unnecessary executables and registry entries. …
- Apply appropriately restrictive permissions to files, services, end points and registry entries.
What is machine hardening?
In computing, hardening is usually the process of securing a system by reducing its surface of vulnerability, which is larger when a system performs more functions; in principle a single-function system is more secure than a multipurpose one. … There are various methods of hardening Unix and Linux systems.
What are the basic steps needed in the process of securing a system?
- Initial Setup and Patching.
- Remove unnecessary Services, Applications, and Protocols.
- Configure Users, Groups, and Authentication.
- Configure Resource Controls.
- Install Additional Security Controls.
- Test the System Security.
Why OS hardening is required?
Most computers offer network security features to limit outside access to the system. … System hardening, also called Operating System hardening, helps minimize these security vulnerabilities. The purpose of system hardening is to eliminate as many security risks as possible.
What is Web application hardening?System hardening is the practice of securing a computer system by reducing its attack surface. … This may involve disabling unnecessary services, removing unused software, closing open network ports, changing default settings, and so on.
Article first time published onWhat is database hardening?
Database hardening is the process of analyzing and configuring your database to address security vulnerabilities by applying recommended best practices and implementing security product sets, processes and procedures.
What is an Application Control?
Application control, a system designed to uniquely identify traffic from various applications on a network, enables an organization to define and apply extremely granular security and network routing policies based upon the source of a particular traffic flow.
How do you harden operating systems and resources?
Operating system hardening: Apply OS updates, service packs, and patches automatically; remove unnecessary drivers, file sharing, libraries, software, services, and functionality; encrypt local storage; tighten registry and other systems permissions; log all activity, errors, and warnings; implement privileged user …
How do you harden a Linux operating system?
- Use Strong and Unique Passwords. …
- Generate an SSH Key Pair. …
- Update Your Software Regularly. …
- Enable Automatic Updates. …
- Avoid Unnecessary Software. …
- Disable Booting from External Devices. …
- Close Hidden Open Ports.
Which of the methods below are effective server hardening techniques?
- Think security from the very start. …
- Configure your security policy. …
- Disable or delete unnecessary accounts, ports and services. …
- Set up appropriate access control to the physical machine and logical components. …
- You’re never finished.
How do I harden my computer?
- Disable Windows 10 automatic login. …
- Set a password with your screensaver. …
- Turn on your firewall. …
- Disable remote access. …
- Enable or install antivirus protection tools. …
- Enable auto-updates for your operating system.
What are five 5 ways to harden a server?
- Keep Your Servers’ Operating Systems Updated. …
- Enforce The Use Of Strong Passwords. …
- Update or Remove Third Party Software. …
- Leverage Local Protection Mechanisms – Fire-walling & Anti-Virus. …
- Advanced Configuration Hardening.
What are some ways to harden a Web server?
- Remove all unnecessary web server modules. …
- Modify the default configuration settings. …
- Turn on additional protection for web applications. …
- Install and run a web application firewall (WAF).
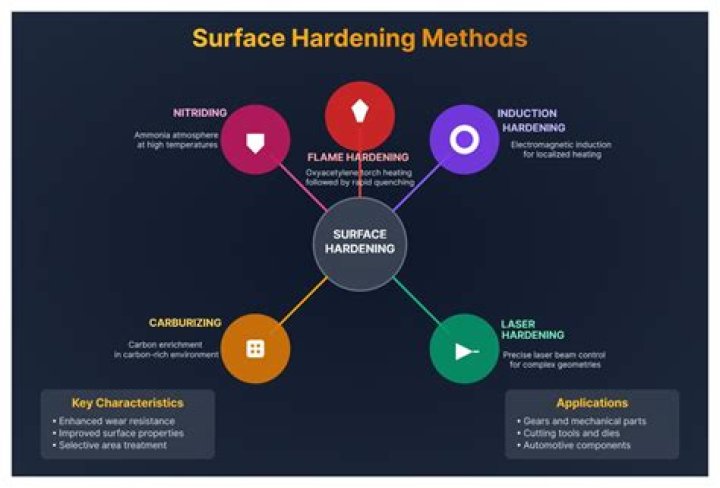
How do you harden steel?
To harden steel, heat the part to be hardened bright red hot again, if possible ‘soak’ it in the heat for a bit, then quench it. It’s the rapid change from red hot to cold that will harden steel. You can use various quenching liquids, but a bucket of water will usually do the trick.
What are the types of hardening?
Each metal hardening process includes three main steps: heating, soaking and cooling the metal. Some common types of hardening include strain hardening, solid solution strengthening, precipitation hardening, and quenching and tempering.
What type of quirk is hardening?
Hardening is a common-tier, transformation-type quirk which allows the user to harden his/her entire/specific part of the body.
How do I keep my operating system and application software secure?
- Keep up with system and software security updates. …
- Have your wits about you. …
- Enable a firewall. …
- Adjust your browser settings. …
- Install antivirus and anti spyware software. …
- Password protect your software and lock your device. …
- Encrypt your data. …
- Use a VPN.
Which is the first step in securing an operating system?
Develop the security policy. The operating system (OS) software must also be secure from any intrusions or attacks. This can be done through a five-step process: The first step being – Develop the security policy. Organizations have security policies that details the steps to be taken to keep the data secure.
What is an important step in securing a host system?
What is an important step in securing a host system? Determining the correct settings and implementing them correctly.
What are 5 key steps that help to ensure database security?
- Principle of least privilege (aka PLP) …
- Platform hardening. …
- Data protection. …
- Monitoring and auditing. …
- Protecting network access using firewalls. …
- Platform isolation. …
- Attack surface management.
What are security best practices?
- Protect your data. …
- Avoid pop-ups, unknown emails, and links. …
- Use strong password protection and authentication. …
- Connect to secure Wi-Fi. …
- Enable firewall protection at work and at home. …
- Invest in security systems. …
- Install security software updates and back up your files.
How do you secure a database application?
- Separate the Database and Web Servers. Always keep the database server separate from the web server. …
- Encrypt Stored Files and Backups. …
- Use a Web Application Firewall (WAF) …
- Keep Patches Current. …
- Enable Security Controls.
What are the four categories of application controls?
Applications reviewed within the Application Control context are divided into four categories: safe, threatening, strong restrictions, and low restrictions.
What are the five types of application control briefly define each?
Application control includes completeness and validity checks, identification, authentication, authorization, input controls, and forensic controls, among others.
What are the three phases of application security?
- Phase I: GRASP. …
- Phase II: ASSESS. …
- Phase III: ADAPT.