What encryption does Kerberos use
Kerberos uses symmetric key cryptography and requires trusted third-party authorization to verify user identities. Since Kerberos requires 3 entities to authenticate and has an excellent track record of making computing safer, the name really does fit.
What is Kerberos and how does it work?
Kerberos is a computer network security protocol that authenticates service requests between two or more trusted hosts across an untrusted network, like the internet. It uses secret-key cryptography and a trusted third party for authenticating client-server applications and verifying users’ identities.
What is Kerberos in security?
Kerberos (/ˈkɜːrbərɒs/) is a computer-network authentication protocol that works on the basis of tickets to allow nodes communicating over a non-secure network to prove their identity to one another in a secure manner.
Is Kerberos always encrypted?
Kerberos is an distributed service that is generally used for secure authentication only. It does neither ensure that a user has the required permissions to access a resource (that would be Authorization) however it may be used to encrypt arbitrary data.What does Kerberos try to solve?
Kerberos was designed to provide secure authentication to services over an insecure network. Kerberos uses tickets to authenticate a user and completely avoids sending passwords across the network.
What are the key benefits of Kerberos?
- Faster authentication. The Kerberos protocol uses a unique ticketing system that provides faster authentication: …
- Mutual authentication. Kerberos supports mutual authentication. …
- Kerberos is an open standard. …
- Support for authentication delegation. …
- Support for the smart card logon feature.
Does Kerberos use TLS?
Kerberos usually does not encrypt transferring data, but SSL and TLS do.
What is the main feature of Kerberos?
The basic features of Kerberos may be put as: It uses symmetric keys.Every user has a password ( key from it to the Authentication Server ) Every application server has a password.Where is Kerberos used?
Kerberos support is built in to all major computer operating systems, including Microsoft Windows, Apple macOS, FreeBSD and Linux. Since Windows 2000, Microsoft has used the Kerberos protocol as the default authentication method in Windows, and it is an integral part of the Windows Active Directory (AD) service.
Why is Kerberos more secure?What makes Kerberos so special? Kerberos uses secret-key cryptography to provide secure communication over non-secure channels. Essentially, Kerberos is a trusted 3rd party server that issues tickets for users so they can authenticate to systems and services.
Article first time published onWhat is the difference between SAML and Kerberos?
SAML is just a standard data format for exchanging authentication data securely using XML Schema, XML signature, XML encryption and SOAP. You would typically use it for a web SSO (single sign on). … Kerberos requires that the user it is authenticating is in the kerberos domain.
Is Kerberos mutual authentication?
Any protocol or service that demands a password is authenticating the user. However, Kerberos provides mutual authentication, so in addition to proving your identity to the server, it proves that the server you are communicating with is what it claims to be.
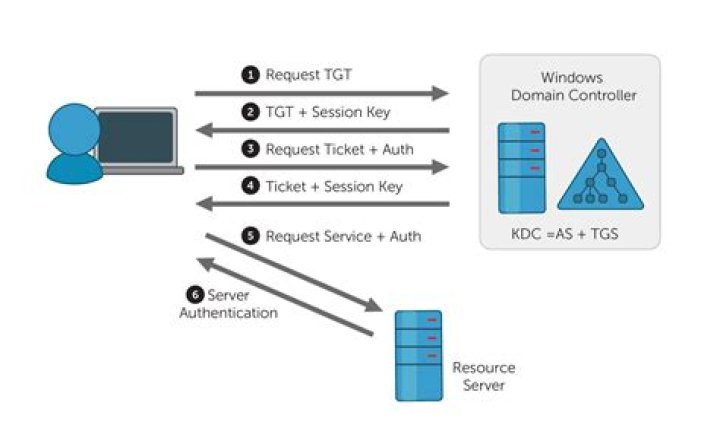
What are the 3 main parts of Kerberos?
Kerberos has three parts: a client, server, and trusted third party (KDC) to mediate between them. Clients obtain tickets from the Kerberos Key Distribution Center (KDC), and they present these tickets to servers when connections are established.
Is Kerberos a SSL?
Kerberos and SSL are both protocols, Kerberos is an authentication protocol, but SSL is an encryption protocol. Kerberos uses UDP, SSL uses (most of the time) TCP. … You’re authenticated by your certificate and the corresponding key. With Kerberos, you can be authenticated by your password or some other way.
Is Kerberos a PKI?
KerberosPKIPassword is required to authenticate users.Private Key is used to authenticate users. The private key is stored on disk, and maintain by users.
Is Kerberos a certificate authority?
The Kerberos Authentication certificate template is the most current certificate template designated for domain controllers and should be the one you deploy to all your domain controllers (2008 or later). The autoenrollment feature in Windows enables you to effortlessly replace these domain controller certificates.
Are there any known weaknesses in Kerberos?
The Kerberos protocol is not as resistant to penetration as it should be. A number of weaknesses are apparent; the most serious is its use of an authen- ticator to prevent replay attacks. The authenticator relies on use of a timestamp to guard against reuse. This is problematic for several reasons.
What are the advantages and disadvantages of Kerberos?
- In Kerberos, Clients and services are mutually authenticated.
- Various operating systems support it.
- Tickets in Kerberos have a limited period. …
- Passwords are never sent over the network unencrypted.
What are the Kerberos limitations?
Biggest lose: assumption of secure time system, and resolution of synchronization required. Could be fixed by challenge-response protocol during auth handshake. Password guessing: no authentication is required to request a ticket, hence attacker can gather equivalent of /etc/passwd by requesting many tickets.
What products use Kerberos?
Perhaps the most widely know products which use Kerberos, are Microsoft Windows and Microsoft Active Directory. In a Microsoft network/domain, users authenticate using the Kerberos protocol when they logon to their Windows workstation.
What is the difference between LDAP and Kerberos?
Kerberos is used to manage credentials securely (authentication) while LDAP is used for holding authoritative information about the accounts, such as what they’re allowed to access (authorization), the user’s full name and uid.
How do you implement Kerberos?
- Create an Active Directory user (you can use an existing one instead). …
- Assign the principal names with the encrypted keys on the domain controller machine. …
- Configure Active Directory delegation. …
- Install and configure the Kerberos client on your machine.
Why is Kerberos more secure than NTLM?
Security. – While both the authentication protocols are secure, NTLM is not as secure as Kerberos because it requires a point-to-point connection between the Web browser and server in order to function properly. Kerberos is more secure because it never transmits passwords over the network in the clear.
Is radius a SAML?
SAML provides a rich, intuitive and consistent login experience. RADIUS interacts with a text-based challenge with inconsistent formatting. Using SAML can reduce user training and support requirements and the consistent sign in experience with SAML makes users less susceptible to phishing attempts.
What is the difference between Radius and Kerberos?
S.No.KerberosRADIUS1.It is called as Kerberos.It is short used for Remote Authentication Dial-In User Service.
What is SSO protocol?
Single Sign-on (SSO) allows a user to use a single set of login credentials – such as a username and password, or even multi-factor authentication – to access multiple applications. This is a Federated Identity Management architecture, sometimes called identity federation.
Why is Kerberos on my Mac?
Kerberos handle the authentication of users trying to access network resources. A user will only get a ticket to access your system if that user is authorized to access your system, you have setup the entire Kerberos infrastructure. If you open a Terminal and run klist -l the credential caches (if any) will be listed.
What is MIT in Kerberos?
Your MIT Kerberos account (sometimes called an Athena/MIT/email account) is your online identity at MIT. Once you set up your account, you will be able to access your MIT email, educational technology discounts, your records, printing services, and much more.
How does Microsoft Kerberos work?
The Kerberos protocol defines how clients interact with a network authentication service. Clients obtain tickets from the Kerberos Key Distribution Center (KDC), and they present these tickets to servers when connections are established. … Both client and server can also be referred to as security principals.
What is Kerberos database?
A Kerberos database contains all of a realm’s Kerberos principals, their passwords, and other administrative information about each principal. … Normally it operates as a network client using Kerberos authentication to communicate with kadmind, but there is also a variant, named kadmin.