What is a Christmas tree scan
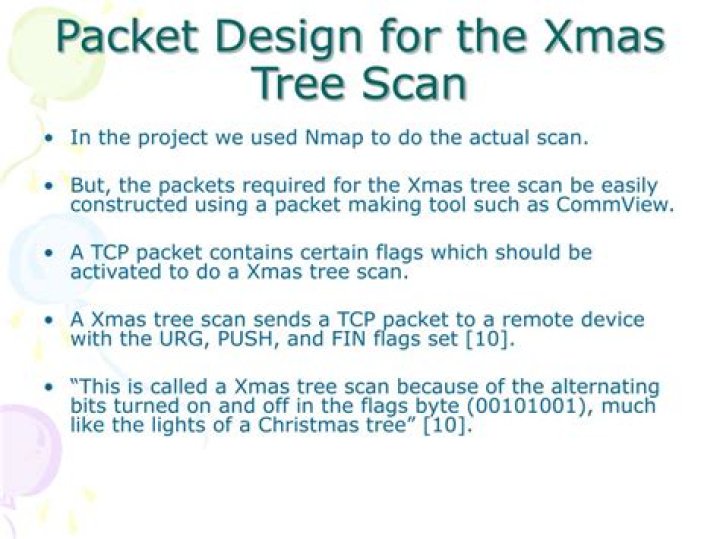
Christmas tree packets can be used as a method of TCP/IP stack fingerprinting, exposing the underlying nature of a TCP/IP stack by sending the packets and then awaiting and analyzing the responses. When used as part of scanning a system, the TCP header of a Christmas tree packet has the flags FIN, URG and PSH set.
What is Xmas attack in cyber security?
A Christmas Tree Attack is a very well known attack that is designed to send a very specifically crafted TCP packet to a device on the network. This crafting of the packet is one that turns on a bunch of flags. There is some space set up in the TCP header, called flags.
What type of packets does an Xmas scan send?
XMAS – XMAS scans send a packet with the FIN, URG, and PSH flags set. If the port is open, there is no response; but if the port is closed, the target responds with a RST/ACK packet. XMAS scans work only on target systems that follow the RFC 793 implementation of TCP/IP and don’t work against any version of Windows.
Why are null FIN and Xmas scans used?
The NULL, FIN, and Xmas scans clear the SYN bit and thus fly right through those rules. Another advantage is that these scan types are a little more stealthy than even a SYN scan. Don’t count on this though—most modern IDS products can be configured to detect them.Why is it called an Xmas scan?
Xmas scans derive their name from the set of flags that are turned on within a packet. These scans are designed to manipulate the PSH, URG and FIN flags of the TCP header. When viewed within Wireshark, we can see that alternating bits are enabled, or “Blinking,” much like you would light up a Christmas tree.
How does a Xmas attack work?
It is a type of attack where a specially crafted TCP packet is sent to the target device. This attack is used as a reconnaissance technique to grab information about various operating systems. … Christmas tree packets are also known as kamikaze packets and lamp test segments.
What is an Xmas scan quizlet?
Xmas Scan. Xmas Scan, attackers send a TCP frame to remote device with FIN, URG, and PUSH flag set. UDP Scanning. use the UDP protocol instead.
What does a FIN scan do?
The FIN scan sends a packet that would never occur in the real world. It sends a packet with the FIN flag set without first establishing a connection with the target. … Again, if no packet is received, the port is considered open and if a RST packet is received, the port is considered closed.What is missing from a half open scan?
A half open does not include the final ACK – a threeway handshake is part of every TCP connection and happens at the beginning of every connection. In the case of a half-open scan, however, a final ACK is not sent, therefore leaving the connection halfway complete.
What is the difference between a SYN scan and a full connect scan?So the difference between these two scan types is TCP Connect scan establish a full connection with the target but SYN scan completes only a half of the connection with target.
Article first time published onWhat is a stealth scan?
A stealth scan (sometimes known as a half open scan) is much like a full open scan with a minor difference that makes it less suspicious on the victim’s device. The primary difference is that a full TCP three-way handshake does not occur.
What is the proper response for a null scan if the port is closed?
Explanation: Closed ports respond to a NULL scan with a reset.
What are the 3 types of network scanning?
- Port Scanning – Detecting open ports and running services on the target host.
- Network Scanning – Discovering IP addresses, operating systems, topology, etc.
- Vulnerability Scanning – Scanning to gather information about known vulnerabilities in a target.
What is Nmap Zenmap?
Zenmap is the Nmap security scanner graphical user interface and provides for hundreds of options. It lets users do things like save scans and compare them, view network topology maps, view displays of ports running on a host or all hosts on a network, and store scans in a searchable database.
What are Xmas packets?
A Christmas tree packet is a type of packet that has a number of special settings applied, which IT experts call “universal” or “default” settings. Christmas tree packets are set up in specific ways to be information heavy and to interact with various protocols in specific ways.
What does the flag do in an Nmap scan?
Add in the -A flag on your Nmap command, you can discover the operating system information of the hosts that are mapped. The -A flag can be used in combination with other Nmap commands. Using the -O flag on your Nmap command will reveal further operating system information of the mapped hosts.
What is Maimon scan?
The Maimon scan is named after its discoverer, Uriel Maimon. According to RFC 793 (TCP), a RST packet should be generated in response to such a probe whether the port is open or closed. … However, Uriel noticed that many BSD-derived systems simply drop the packet if the port is open.
What is one reason for using a scan like an ACK scan?
UDP will retransmit more. What is one reason for using a scan like an ACK scan? It may get through firewalls and IDS devices.
What is the difference between a SYN scan and a full connect scan quizlet?
A SYN scan sends the first SYN message and then responds with a RST message after receiving the SYN/ACK from the target. A full connect scan completes the three-way handshake before sending the RST message.
What is Fragroute primarily used for?
Fragroute intercepts, modifies and rewrites egress traffic destined for the specified host. Simply frag route fragments packets originating from our(attacker) system to the destination system. Its used by security personnel or hackers for evading firewalls, avoiding IDS/IPS detections & alerts etc.
What is null scan in nmap?
A Null Scan is a series of TCP packets that contain a sequence number of 0 and no set flags. … If the port is closed, the target will send an RST packet in response. Information about which ports are open can be useful to hackers, as it will identify active devices and their TCP-based application-layer protocol.
How do you perform a SYN scan?
In SYN scanning, similar to port scanning, the threat actor attempts to set up a Transmission Control Protocol/Internet Protocol (TCP/IP) connection with a server at every possible port. This is done by sending a SYN (synchronization) packet, as if to initiate a three-way handshake, to every port on the server.
What is SYN message?
What Are SYN packets? … SYN packets are normally generated when a client attempts to start a TCP connection to a server, and the client and server exchange a series of messages, which normally runs like this: The client requests a connection by sending a SYN (synchronize) message to the server.
What does SYN received mean?
SYN-RECEIVED is a Packet within the Transmission Control Protocol (TCP) where the server has sent a SYN-ACK and is waiting for a confirming ACK.
What is aggressive scanning?
Aggressive mode enables OS detection ( -O ), version detection ( -sV ), script scanning ( -sC ), and traceroute ( –traceroute ). This mode sends a lot more probes, and it is more likely to be detected, but provides a lot of valuable host information.
What is a potential mistake when performing a ping sweep on a network?
What is a potential mistake when performing a ping sweep on a network? … Fping doesn’t allow pinging multiple IP addresses simultaneously. False. Ports that aren’t listening or responding to a packet.
What can the attacker infer about the status of the port when a FIN scan is performed?
An adversary uses a TCP FIN scan to determine if ports are closed on the target machine. … An adversary uses the response from the target to determine the port’s state. If no response is received the port is open. If a RST packet is received then the port is closed.
What are the TCP three-way handshake method used in a TCP connect scan?
The TCP handshake TCP uses a three-way handshake to establish a reliable connection. The connection is full duplex, and both sides synchronize (SYN) and acknowledge (ACK) each other. The exchange of these four flags is performed in three steps: SYN, SYN-ACK, ACK, as shown in Figure 5.8.
Why do you get open filtered from Nmap on some scans?
open|filtered : Nmap places ports in this state when it is unable to determine whether a port is open or filtered. This occurs for scan types in which open ports give no response. The lack of response could also mean that a packet filter dropped the probe or any response it elicited.
What is the purpose of 3 way handshaking?
A three-way handshake is primarily used to create a TCP socket connection to reliably transmit data between devices. For example, it supports communication between a web browser on the client side and a server every time a user navigates the Internet.
What is a UDP scan?
UDP scanning methods involve sending a UDP datagram to the target port and looking for evidence that the port is closed. Open UDP ports usually do not respond to UDP datagrams as there is no stateful mechanism within the protocol that requires building or establishing a session.