Where should you implement IPS in your IT infrastructure
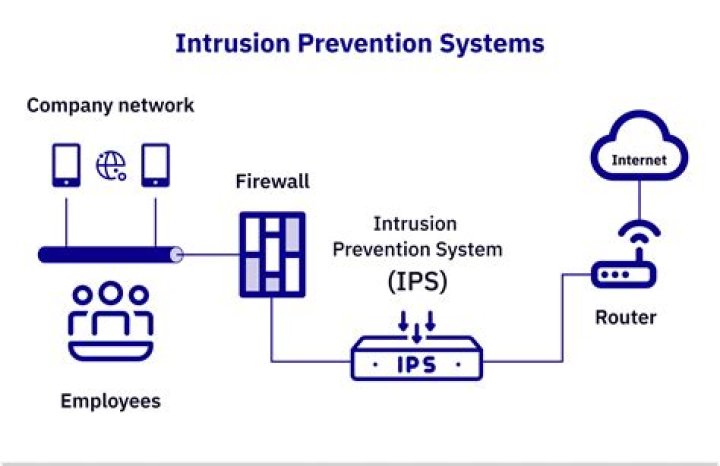
It’s generally accepted that intrusion prevention systems should be implemented at the edge of the network directly behind the firewall and in front of the server(s.) This enables the firewall to perform its duties and block or filter out the majority of malicious traffic.
Where should an intrusion detection system be placed?
An intrusion detection system is placed behind a firewall but before the router. This location maximizes effectiveness, as the firewall can handle different types of threats to an IDS, and both will want to be in front of the router so that malicious data does not reach the users.
Where can I implement IDS and IPS?
Placement of the IDS device is an important consideration. Most often it is deployed behind the firewall on the edge of your network. This gives the highest visibility but it also excludes traffic that occurs between hosts.
Where do you place an IPS?
The IPS often sits directly behind the firewall and provides a complementary layer of analysis that negatively selects for dangerous content.How can an intrusion prevention system be implemented?
- IDS, IPS and hybrid modes. Your IPS should be multifunctional so you can deploy it depending on your exact need. …
- AET protection. …
- Event correlation. …
- Web filtering. …
- SSL inspection. …
- Denial-of-service protection. …
- Central management capabilities. …
- Performance.
What is IPS network security?
An intrusion prevention system (IPS) is a network security tool (which can be a hardware device or software) that continuously monitors a network for malicious activity and takes action to prevent it, including reporting, blocking, or dropping it, when it does occur.
Why the intrusion detection system IDS is generally placed after the firewall?
Placing the IDS in this location allows it to do its job on all traffic that gets through the edge firewall and provides an extra layer of protection for the DMZ, which is the most vulnerable part of your network since it contains your public servers such as Internet-accessible Web servers, DNS servers, front-end mail …
Is IPS a firewall?
Intrusion Prevention Systems (IPS): live in the same area of the network as a firewall, between the outside world and the internal network. IPS proactively deny network traffic based on a security profile if that packet represents a known security threat.Does the IPS go in the DMZ?
If you have a large network, common places to deploy an IPS would be inside of your edge/border/transit routers on the outer border of your DMZ or border of your inner private network.
How do I set up an IPS?To configure the global options of IPS, take the following steps: On the Navigation pane, click Configure > Security > IPS to visit the IPS page. On the Task tab in the right auxiliary pane, configure the options in the IPS Global Configuration section. IPS: Select/clear the Enable check box to enable/disable IPS.
Article first time published onWhy do we need IDS with IPS?
If an IPS is a control tool, then an IDS is a visibility tool. Intrusion Detection Systems sit off to the side of the network, monitoring traffic at many different points, and provide visibility into the security posture of the network. … In the hands of a security analyst, the IDS becomes a window into the network.
How does an IPS differ from a firewall?
An IPS will inspect content of the request and be able to drop, alert, or potentially clean a malicious network request based on that content. … A firewall will block traffic based on network information such as IP address, network port and network protocol.
Do IDS and IPS work together?
IDS and IPS work together to provide a network security solution. … In the process of detecting malicious traffic, an IDS allows some malicious traffic to pass before the IDS can respond to protect the network.
Where is an IPS commonly placed in a network in front of the firewall in line with the firewall behind the firewall on the end users device?
To do this, an IPS tool will typically sit right behind a firewall, acting as an additional layer that will observe events for malicious content. In this way, IPS tools are placed in direct communication paths between a system and network, enabling the tool to analyze network traffic.
Why IDS and IPS are critical for cybersecurity?
Why IDS/IPS Systems are Critical for Cybersecurity According to research, your website is hit with 22 cyber attacks every day. IDS/IPS ensures any potential threats that sneak through the firewall are addressed as soon as the attack occurs.
Can IPS prevent DDoS?
Typical IPS devices also claim some anti- DDoS protection. While it is true they can (and do) incorporate some basic protection, the majority of current IPS products evolved from software-based solutions that were signature-based.
Why do we need IPS when we have firewall?
Firewalls and IPSes are control devices. They sit inline between two networks and control the traffic going through them. This means that the IPS is in the policy side of your security house. … The main reason to have an IPS is to block known attacks across a network.
What is the role of an IPS CCNA?
Answers Explanation & Hints: An intrusion prevention system (IPS) provides real-time detection and blocking of attacks.
What is IDS IPS which layer in OSI does it work?
As part of the OSI Layer 3 (network layer), IDS and IPS use a dynamically updated signature database to verify legitimate network traffic and block any detected network activity abnormalities.
What are the four 4 types of approaches used by IPS for securing the network from intrusions?
- Network-based intrusion prevention system (NIPS): …
- Wireless intrusion prevention system (WIPS): …
- Network behavior analysis (NBA): …
- Host-based intrusion prevention system (HIPS):
How does IPS work in checkpoints?
Intrusion Prevention Systems detect or prevent attempts to exploit weaknesses in vulnerable systems or applications, protecting you in the race to exploit the latest breaking threat. Check Point IPS protections in our Next Generation Firewall are updated automatically.
What is IPS in Sophos firewall?
Sophos Intrusion Prevention System (IPS) is an advanced firewall feature that protects your network. The downside is that IPS is a resource-intensive process, as it needs to match every packet with thousands of attack signatures.
What should my DMZ host IP address be?
You should assign the DMZ host an IP address in the same subnet as the RV110W’s LAN IP address, but it cannot be identical to the IP address given to the LAN interface of this gateway. To configure DMZ: Choose Networking > LAN > DMZ Host. Check the Enable check box to enable DMZ on the network.
What are the disadvantages of DMZ?
Disadvantages. Setting up the DMZ is something that not everyone knows how to do, so doing it the wrong way can lead to the possibility of lose or suffer from some kind of copy in all the information that the system has.
Should I enable DMZ?
DMZ should only be used if you have a computer/device that cannot run Internet applications properly from behind the router.
Which is better firewall or IPS?
The main difference being that firewall performs actions such as blocking and filtering of traffic while an IPS/IDS detects and alert a system administrator or prevent the attack as per configuration. … IPS is a device that inspects traffic, detects it, classifies and then proactively stops malicious traffic from attack.
Does IPS officer get security?
Security for VIP’s: IPS officers are often responsible for the security of VIP’s especially for protection of Chief Ministers and Prime minister as well.
What is IPS in Cisco?
Cisco IOS Intrusion Prevention System (IPS) is an inline, deep-packet inspection feature that effectively mitigates a wide range of network attacks.
How do I run Suricata in IPS mode?
- Install Netfilter packages: …
- Configure Suricata with –enable-nfqueue option.
- Build and install.
- Configure iptables. …
- Configure Suricata NFQ modes in the suricata. …
- Start Suricata to filter packets in NFQUEUE :
Is Suricata better than snort?
One of the main benefits of Suricata is that it was developed much more recently than Snort. … Fortunately, Suricata supports multithreading out of the box. Snort, however, does not support multithreading. No matter how many cores a CPU contains, only a single core or thread will be used by Snort.
What is pfSense snort?
Snort is an intrusion detection and prevention system. It can be configured to simply log detected network events to both log and block them. … The package is available to install in the pfSense® webGUI from System > Package Manager. Snort operates using detection signatures called rules.